Enterprise Mobility and Management (EMM, MDM, MAM, BYOD):
Managing mobile apps and devices has become a big challenge that is still being faced by all different types of organizations these days. One technology that's evolved to address mobile security, access and control is Enterprise Mobility Management (EMM) and moving more towards a trend of BYOD.
EMM was an evolution of Mobile Device Management (MDM) and allowing all companies work forces moving towards mobility, strength and gaining increase security.
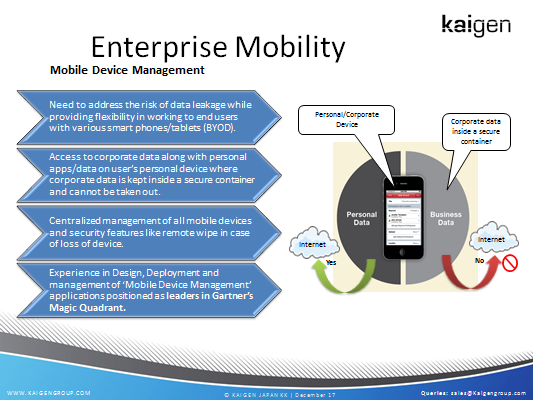
The BYOD concept encouraged employees bringing their own devices to work and increased the challenges for organizations to maintain secure access of their networks and data. Mobile device management (MDM) was the initial response to the challenge and focused on the device enrollment and access. Mobile application management (MAM) also speeded to control data and applications on mobile devices.
All these technologies have been superseded by enterprise mobility management, a sophisticated technology that combines MDM and MAM, offering access, data protection, app management, threat management, separation of personal and work data, and visibility and control.
At the most basic level, there are five core capabilities that all organizations need from any EMM solution:
Secure Mail and Secure Access: Providing the ability for mobile user�s work force to work from wherever, whenever with secured accessall the applications and data. It's essential that organizations help their users to securely access applications while maintaining proper security controls.
Tracking and Visibility: Understanding what's running on mobile devices is the key to creating compliance policies and being able to detect potential risks. Simply put, if you don't know what's running, how can you control the risk? Having the visibility in mind, we need to have better tracking and perform necessary actions whenever compliance is violated.
Regular office work: Even after mobilizing with any solution of your choice there has to be a complete mechanism for the users to at least perform their daily tasks without even a need of using a desk and a computer within or outside the office premises. Example: Basic needs like, Email, Printing, Network drives, data sharing / editing and many more.
Data protection: Malware spread though your email attachments or through web access, the best EMM solutions provide anti-malware and data protection capabilities to help limit the risk of breaches and data loss depending on each type of solution.
Increased efficiency with Cost reduction: Cost is always a main factor when you want to increase the efficiency. Choosing the right EMM platform that allows end to end delivery of the solution, Access from wherever and whenever allows users to use BYOD and enhance the efficiency to process any work and deliver it to the back end office along with the reduction of your Infrastructure in various ways.
Looking beyond the basics, some of the advanced features of EMM are:
Kaigen Offerings:
At Kaigen, we have a team of solution Architects with experience of implementing EMM solutions from all the top leaders in the market. We believe in not only implementing but also analyzing your needs and select the right technology amongst the top EMM leaders to provide an overview of key features that organizations need so they can deploy mobility, control mobility and limit the security intrusions. Kaigen will enable you:

